Audit & Compliance
Every request, every policy decision, every threat detection, every configuration change -- INS captures a complete, tamper-evident audit trail for your AI agent infrastructure. Built for SOC 2, ISO 27001, and enterprise governance requirements.
Why AI Agent Audit Matters
When AI agents call tools, access databases, and execute actions on behalf of users, traditional application logging is no longer sufficient. You need to know which agent called which tool, what parameters were sent, whether the request was allowed or blocked, and why. Without this visibility, compliance auditors, incident responders, and security teams are flying blind.
INS captures structured audit events at every decision point in the MCP request lifecycle. Each event includes the actor identity, the resource affected, the action taken, contextual details, the originating IP address, and a precise timestamp. Events are recorded asynchronously so audit logging never blocks or slows down the critical request path.
This is not just logging -- it is a purpose-built audit system designed for compliance frameworks that require demonstrable access controls, change tracking, and incident documentation.
Comprehensive Event Coverage
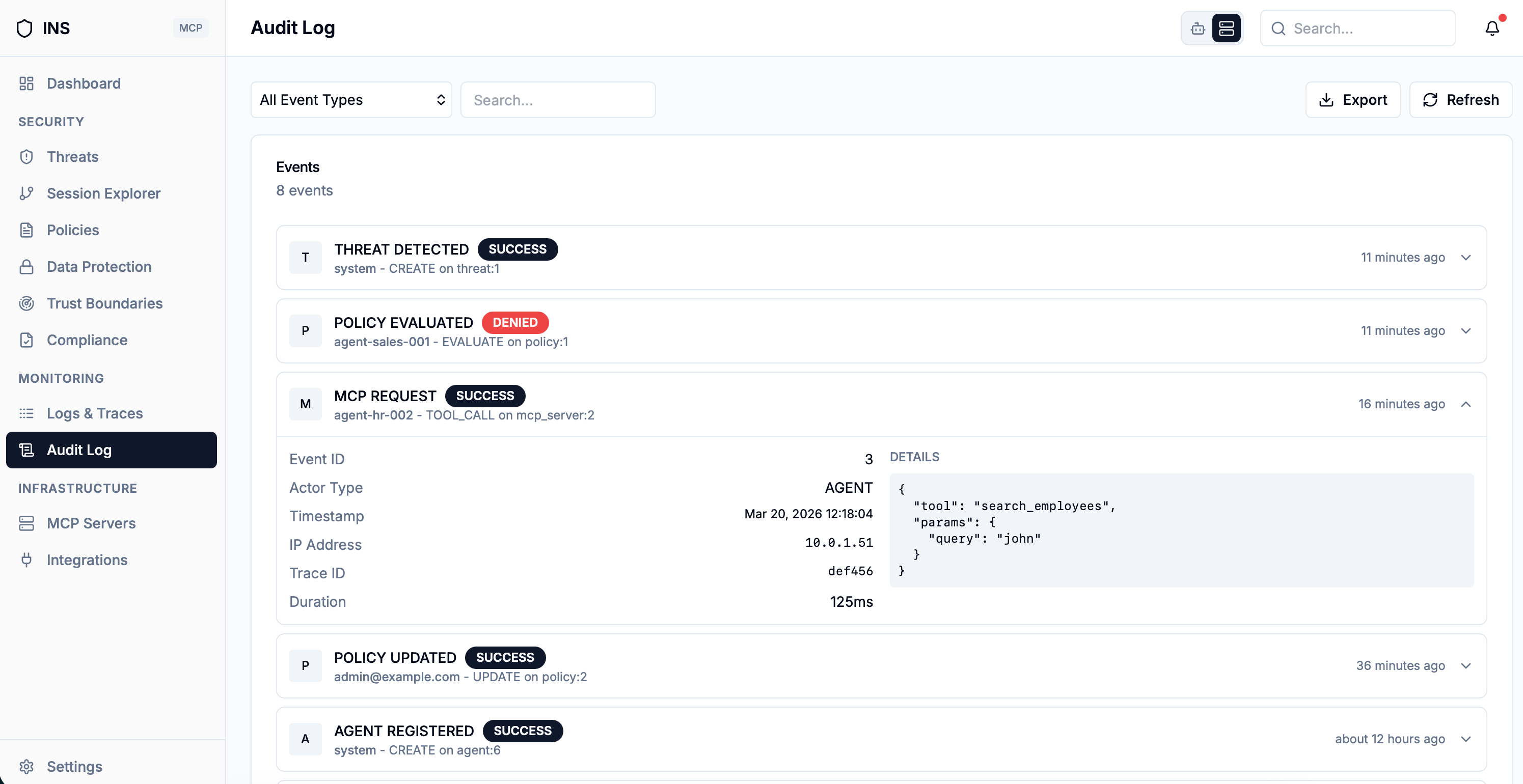
INS tracks a broad taxonomy of event types across requests, policies, servers, agents, security incidents, and administrative actions. Every category maps directly to compliance control objectives.
Request Events
Every MCP request is logged with its outcome: REQUEST_RECEIVED, REQUEST_ALLOWED, REQUEST_BLOCKED, MCP_REQUEST, and TOOL_CALL events capture the full request lifecycle.
Security Events
THREAT_DETECTED events record every blocked attack. LOGIN_SUCCESS and LOGIN_FAILURE track authentication. DLP_DETECTION logs sensitive data findings.
Configuration Changes
Policy creation, updates, and deletions. MCP server registration and removal. Agent provisioning. Trust boundary modifications. DLP detector changes. Every administrative action leaves a trail.
User Management
USER_CREATED, USER_UPDATED, USER_INVITED, and USER_REMOVED events track all identity lifecycle operations for access control audits.
Scan Events
SCAN_TRIGGERED and POLICY_CHECK events document every security evaluation, providing evidence of continuous monitoring for compliance reviews.
Integration Events
INTEGRATION_ENABLED, INTEGRATION_DISABLED, and INTEGRATION_UPDATED events track changes to external integrations and data flows.
Structured Event Data
Every audit event in INS is a structured record with well-defined fields. Each event captures the event type, the actor who performed the action, the resource type and ID affected, the action taken, a flexible details map for contextual metadata, the originating IP address, and the creation timestamp.
The details map is particularly powerful: it captures service and method information, resource descriptions, status changes, policy scope and severity, server URLs and health status, agent types and external IDs, trust boundary configurations, DLP detector settings, user roles, and more. This contextual richness means you can answer forensic questions without needing to correlate across multiple log sources.
Audit events are multi-tenant by design. Each event is scoped to an account ID, ensuring tenant isolation in shared deployments. Filtering supports event type, date ranges, and pagination for efficient querying across large datasets.
AuditEvent Fields
- eventType -- categorized event type (e.g. THREAT_DETECTED, POLICY_CREATED)
- actor -- the authenticated user or "system" for automated actions
- resourceType / resourceId -- what was affected (POLICY, AGENT, MCP_SERVER, etc.)
- action -- what happened (CREATE, UPDATE, DELETE, BLOCKED, SUCCESS)
- details -- flexible map with contextual metadata specific to each event type
- ipAddress -- source IP for access origin tracking
Nothing Slips Through
Audit capture is built into every part of INS by design. When INS is deployed, every action that touches a tool, a policy, an agent, or a server is recorded automatically. There is no opt-in flag, no manual logging step, and no way for a developer to forget to instrument a new feature.
This guarantees that compliance evidence is always complete. Auditors never see "we forgot to log that endpoint" gaps because the audit layer is part of the architecture, not an afterthought.
No Performance Penalty
Audit events are recorded asynchronously, off the critical request path. Even under heavy load, every event is captured -- but agents never wait for the audit system. Latency stays predictable, and the audit system scales independently of request traffic.
This separation matters in production. Traditional audit approaches force a tradeoff: log everything and slow down, or skip events to stay fast. INS does both -- complete coverage with no measurable overhead on tool calls.
Filter by event type, date range, severity, or actor. Search across event details. Aggregate counts and trends over any time period. Everything you need for compliance reports, audit reviews, and incident investigations is queryable in real time.
Compliance Dashboard & Reporting
The audit stats API provides real-time compliance metrics. For any configurable time period (24 hours, 7 days, 30 days, or 90 days), INS computes total event counts, policy action breakdowns, success vs. failure ratios, threat event counts, and events grouped by type. These metrics map directly to compliance control evidence requirements.
Event Analytics
Total events, events by type, success/failure ratios, and policy action counts are computed in real time. Filter by 24h, 7d, 30d, or 90d periods for trend analysis.
Paginated Search
Filter audit events by type, date range, and pagination. Full-text search across event details. Export-ready for auditor review and regulatory submissions.
How It Works
Capture
Every action against a tool, policy, agent, or server is recorded automatically. No manual instrumentation required for new features.
Publish
Events are recorded asynchronously off the critical request path. Agents never wait for audit logging — latency stays predictable under load.
Persist
Events are stored durably with full event metadata, ready for compliance queries, filters, and long-term retention.
Report
The audit API provides real-time stats, filtered event lists, and aggregated metrics for compliance dashboards and auditor reviews.
Demonstrate Compliance for Your AI Agent Infrastructure
Join the waitlist to get early access to INS and build a complete audit trail for every AI agent action in your organization.
Join the Waitlist