Policy Engine
Define exactly which agents can access which tools, under what conditions, and what happens when rules are violated. INS Policy Engine gives you fine-grained control over every MCP interaction with 4 action types and 7 condition operators.
Why AI Agents Need Policy Enforcement
AI agents operate autonomously, making decisions and calling tools without human oversight for each individual action. In a traditional application, access control is enforced at the API layer with well-understood patterns. But MCP introduces a new paradigm: agents dynamically discover and invoke tools across multiple servers, often with parameters they construct on their own.
Without policy enforcement, any agent with MCP access can call any tool on any server at any time. A coding assistant agent could access database administration tools. A customer service agent could invoke deployment pipelines. An analytics agent could read sensitive HR data. The attack surface expands with every new tool and server you connect.
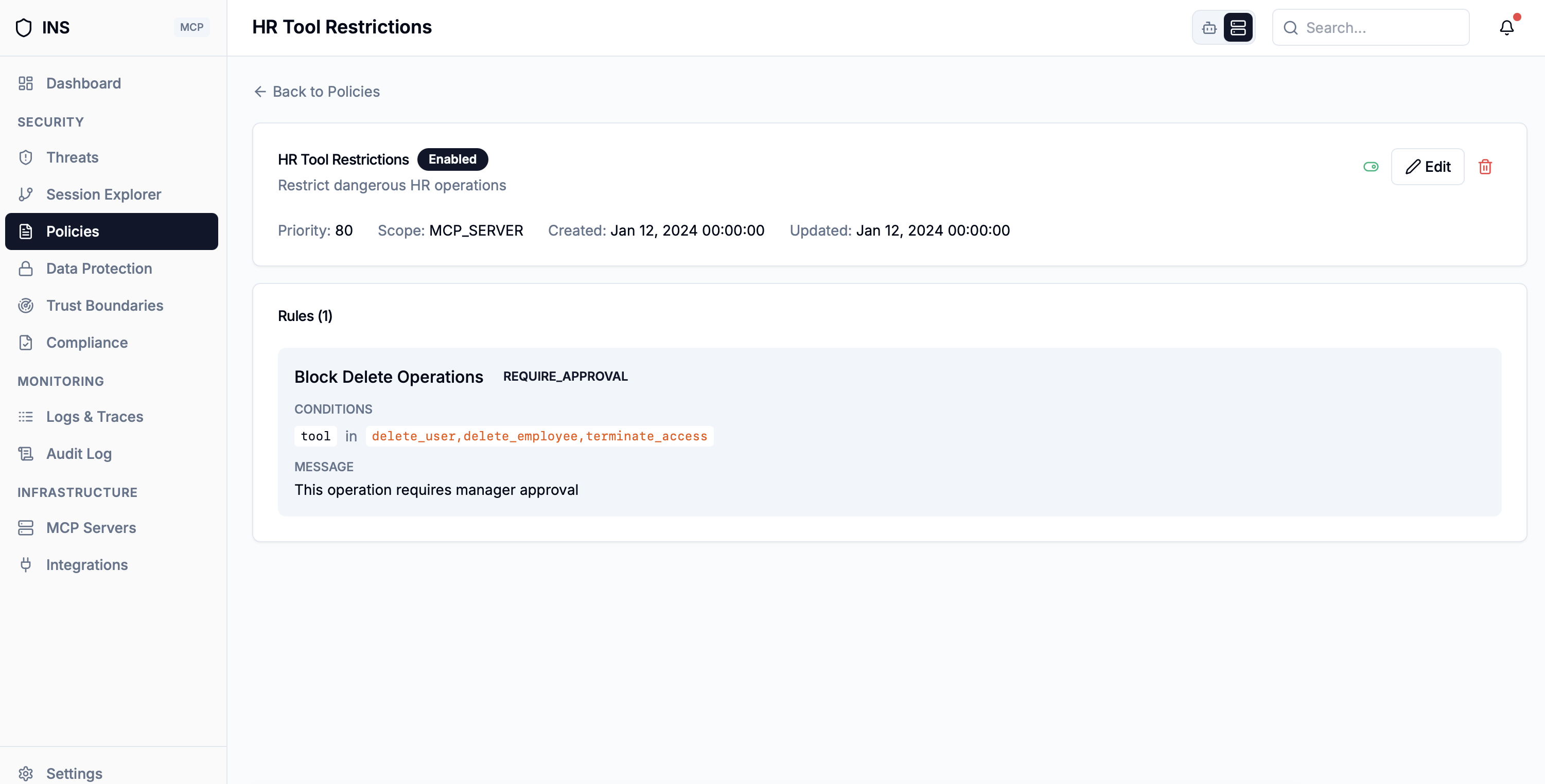
The INS Policy Engine sits at the gateway layer, evaluating every tool call against your defined rules before it reaches the MCP server. Policies are evaluated in priority order (highest first). DENY and REQUIRE_APPROVAL actions return immediately, while MASK and NOTIFY results are aggregated across all matching policies. This gives you deterministic, auditable control over your entire MCP infrastructure.
4 Policy Actions
Each policy rule specifies an action that INS takes when the rule's conditions match an incoming request. Actions range from notification to hard blocking. Requests that match no policy rules are allowed by default.
Deny
Blocks the request immediately and returns an error to the agent. The denial is logged with the policy name and matched conditions for audit. Takes highest precedence.
Require Approval
Holds the request in a pending queue until a human reviewer approves or rejects it. Ideal for high-risk operations like database writes or access to sensitive systems.
Mask
Allows the request but sanitizes the response before returning it to the agent. Sensitive fields are redacted based on the policy configuration, enabling partial data access.
Notify
Allows the request to proceed but sends a notification to the configured channel and creates a detailed audit entry. Use during initial rollout to observe access patterns before enforcing.
7 Condition Operators
Policy conditions define when a rule applies. Each condition consists of a field, an operator, and a value. Multiple conditions can be combined within a rule using AND logic -- all conditions must match for the rule's action to execute.
| Operator | Description |
|---|---|
equals | Exact match comparison |
not_equals | Inverse of exact match |
contains | Substring match within the field value |
not_contains | Inverse substring match |
starts_with | Prefix matching for field values |
ends_with | Suffix matching for field values |
regex | Full regular expression matching |
Condition Fields
Condition fields specify what part of the request to evaluate. INS evaluates fields from the MCP request context to determine which policies apply.
Identity Fields
Control access based on which agent is making the request and which MCP server it targets.
Operation Fields
Restrict which tools, aliases, and MCP methods an agent can invoke.
Policy Templates for Common Scenarios
INS includes ready-to-use policy templates for the most common security scenarios. Start with a template and customize it to match your organization's requirements.
Least Privilege Access
Default-deny policy that only allows agents to access tools explicitly listed in their permission set. New tools require manual approval before any agent can invoke them.
Block Dangerous Tools
Deny access to tools whose names contain write-operation keywords (delete, drop, alter, deploy). Uses substring matching to catch variations without maintaining an exact list.
Observe New Agents
Use the notify action for newly onboarded agents. All their tool calls proceed but generate alerts, letting you build a baseline before switching to deny or require_approval.
Deployment Approval Gate
Routes all deployment-related tool calls through human approval. CI/CD tools, container orchestration, and infrastructure provisioning require a reviewer sign-off.
How It Works
Define
Create policies with rules, conditions, and actions through the INS dashboard or API. Set priority to control evaluation order.
Match
Every incoming request is evaluated against active policies sorted by priority. DENY and REQUIRE_APPROVAL return immediately; MASK and NOTIFY are aggregated.
Enforce
The matched action executes: deny, hold for approval, mask response, or notify. Requests matching no policy are allowed by default.
Monitor
Every policy evaluation is logged. The dashboard shows which policies fire most often, helping you tune rules over time.
Take Control of Your AI Agent Workflows
Join the waitlist to define and enforce security policies across your entire MCP infrastructure. Gain visibility and control over every agent interaction.
Join the Waitlist